Berkine
Amazon Rekognition Video - Deep Learning Powered Video Recognition Services
- Created: 20/08/2020
- by: Berkine
Welcome! First of all we want to thank you for purchasing our Amazon Rekognition Video Application
We really do appreciate every sale. If you like our work please do not forget to rate it. It helps us in developing new and better items

In the following sections we will explain how to set up and use it the easiest way possible. If you have any questions that you feel should have been in this document you can contact us through our profile page on codecanyon.net/user/berkine and we'll get back to you as soon as possible. Thanks so much!!!
For questions on basic HTML, JavaScript or CSS editing - please give your question a quick Google or visit W3Schools as template issues get top priority. You will need some knowledge of HTML/JS/PHP/CSS to edit this file uploader.
Amazon Rekognition Video Information
Amazon Rekognition Video makes it easy to add image and video analysis to your applications using proven, highly scalable, deep learning technology that requires no machine learning expertise to use. With Amazon Rekognition, you can identify objects, people, text, scenes, and activities in images and videos, as well as detect any inappropriate content. Amazon Rekognition also provides highly accurate facial analysis and facial search capabilities that you can use to detect, analyze, and compare faces for a wide variety of user verification, people counting, and public safety use cases.
With Amazon Rekognition, you can identify thousands of objects (such as bike, telephone, building), and scenes (such as parking lot, beach, city). When analyzing video, you can also identify specific activities such as "delivering a package" or "playing soccer".
Amazon Rekognition helps you identify potentially unsafe or inappropriate content across both image and video assets and provides you with detailed labels that allow you to accurately control what you want to allow based on your needs. Use Amazon A2I to enhance the accuracy of Amazon Rekognition image moderation predictions using human review.
AWS PHP SKD Installation (Version 3)
The AWS PHP SDK v3 comes included in the app - "vendor" folder in the root directory of the app is the offical AWS PHP SDK
If you want to install AWS PHP SDK by yourself, you can visit the following link for the up to date instructions regarding installation of AWS PHP SDK v3 and its new versions directly from Amazon Web Services page
General Settings Configuration
In order to run Amazon Rekognition - you need to update the following lines accordingly:
Create AWS IAM User with Amazon Rekognition Full Access and Amazon S3 Bucket Full Access Policies attached (Explained in Step 2 of Batch Translate setup).
Download and save Access Key and Secret Access Key of the User
Create Amazon S3 bucket for uploading (video files)
Make sure you are using the AWS Region where Amazon Rekognition is available, you can check from here whether or not your AWS Region supports Amazon Translate: Check Service Availability
- For creating AWS IAM user please visit - Create AWS IAM User section
- For creating Amazon S3 Bucket please visit - Create Amazon S3 Bucket section
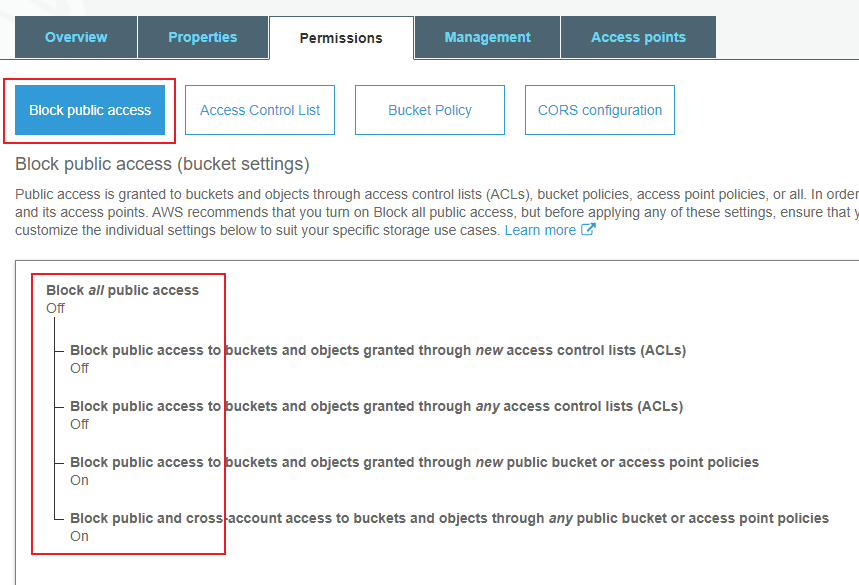
A - Provide Public Access to the S3 bucket or at least turn off first 2 points as shown in the picture:

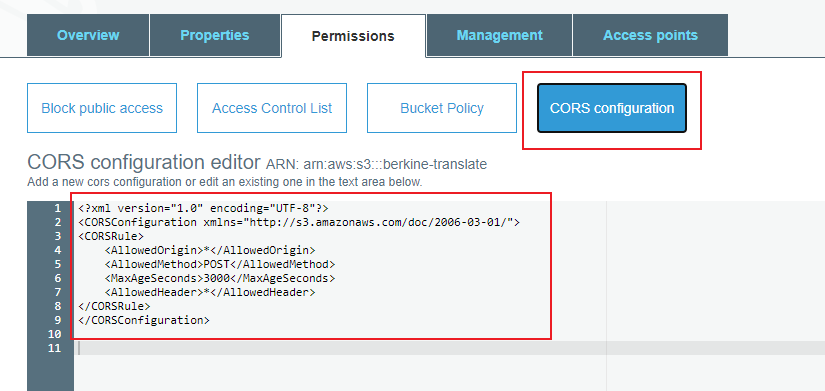
B - Set CORS Configuration as shown in the picture:

Edit the 'config.php' file accordingly:
- Provide AWS IAM Access Key and Secret Access Key:
return [ 'polly' => [ 'accessKey' => 'XXXXXXXXXXXXX', # IAM User Access key 'secretAccessKey' => 'XXXXXXXXXXXX', # IAM User Secret Access key 'region' => 'XX-XXXX-X', # AWS Region (selected data center) 'version' => 'latest', 'bucketName' => 'XXXXXXXX' # Amazon S3 Bucket Name (must be unique, bucket must be in the same region as Rekognition used) ] ];
Provide AWS IAM Access Key and Secret Access Key into the code
return [ 'polly' => [ 'accessKey' => 'XXXXXXXXXXXXXXXXXXXX', # IAM User Access key (in case if you want to hard code directly ) 'secretAccessKey' => 'XXXXXXXXXXXXXXXXXXXXXXXXXXXXX', # IAM User Secret Access key (in case if you want to hard code directly) /* 'region' => 'XX-XXXX-X', */ # AWS Region (selected data center) /* 'version' => 'latest', */ /* 'bucketName' => 'XXXXXXXXXXXX' */ # Amazon S3 Bucket Name (must be unique, bucket must be in the same region as Rekognition used) ] ];
Provide Amazon S3 Bucket name to which create IAM user has write and read permissions
return [ 'polly' => [ /* 'accessKey' => 'xxxxxxxxxxxxxx', */ # IAM User Access key (in case if you want to hard code directly ) /*'secretAccessKey' => 'xxxxxxxxxxxxxxxx', */ # IAM User Secret Access key (in case if you want to hard code directly) /* 'region' => 'XX-XXXX-X', */ # AWS Region (selected data center) /* 'version' => 'latest', */ 'bucketName' => 'XXXXXXX' # Amazon S3 Bucket Name (must be unique, bucket must be in the same region as Rekognition used) ] ];
Provide AWS Region code that you are using, make sure you are using the AWS Region where Amazon Rekognition Video is available, you can check from here whether or not your AWS Region supports Amazon Rekognition Video: Check Service Availability
return [ 'polly' => [ /* 'accessKey' => 'xxxxxxxxxxxx', */ # IAM User Access key (in case if you want to hard code directly ) /*'secretAccessKey' => 'xxxxxxxxxxxx', */ # IAM User Secret Access key (in case if you want to hard code directly) 'region' => 'XX-XXXX-X', # AWS Region (selected data center) /* 'version' => 'latest', */ /* 'bucketName' => 'XXXXXXX' */ # Amazon S3 Bucket Name (must be unique) ] ];
Amazon Rekognition Video Setup
Amazon Rekognition Video requires SNS Topic create and IAM Role to allow Rekognition use SNS service.
Steps to setup up Rekognition Video:
- Step 1: Configure your S3 Bucket
- Step 2: Create IAM user with Rekognition and S3 Policies attached, if you already create an IAM user with these policies then proceed to the next step
- Step 3: Create a SNS Topic
- Step 4: Create a Role for Rekognition to access SNS Service
- Step 5: By itself your Rekognitin Video code cannot call assigned Role from Step 4, that is why we need assume the role permission. It will be last step of IAM user configuration.
- Step 6: Configure Rekognition.php
- Step 7: Webcam Configuration
Step 1
Configure your S3 Bucket
Make your S3 bucket publicly accessible, make sure you have at least first 2 options turned off or all of them
Add CORS settings to you S3 Bucket so that your browser can access it
Step 2
Create IAM role that allows him to use Amazon Rekognition service and provides access to an S3 Bucket
Select User and click Create New User
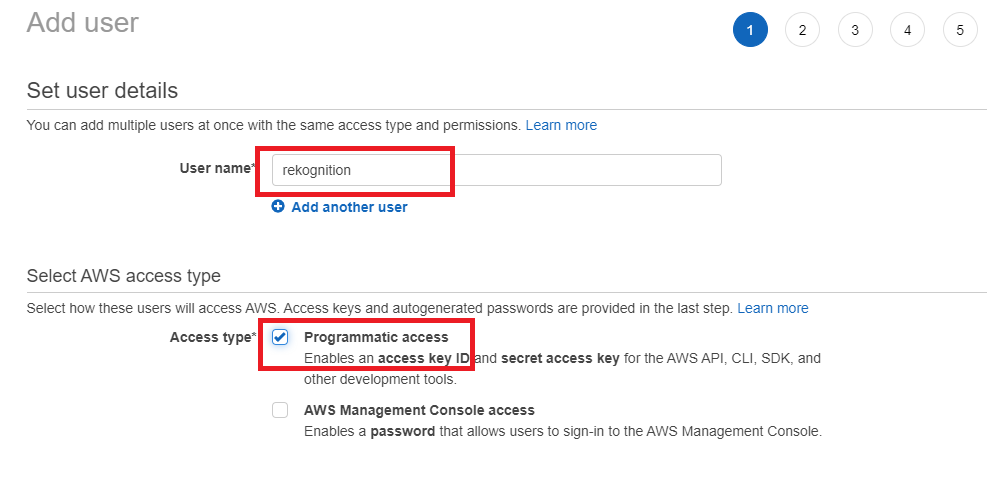
Enter a User name and select Programmitc Access, follow to the next steps and store your Access Key and Secret Access Keys in a secure place
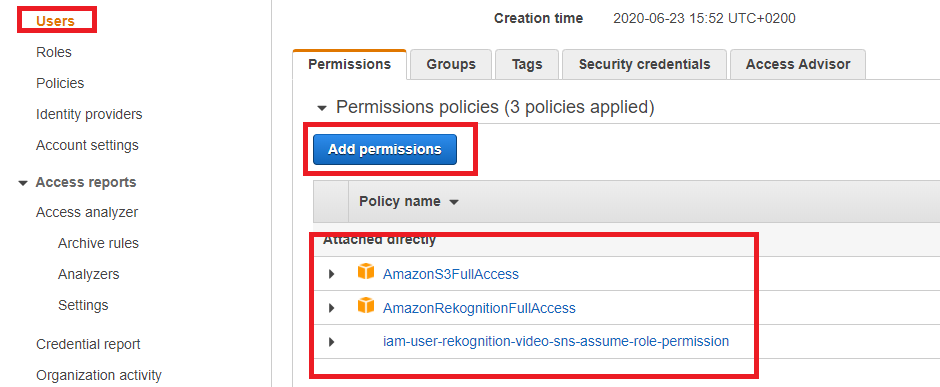
Select your newly created user and click on Add Permissions
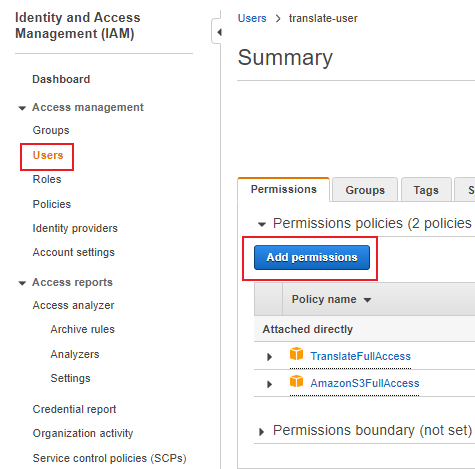
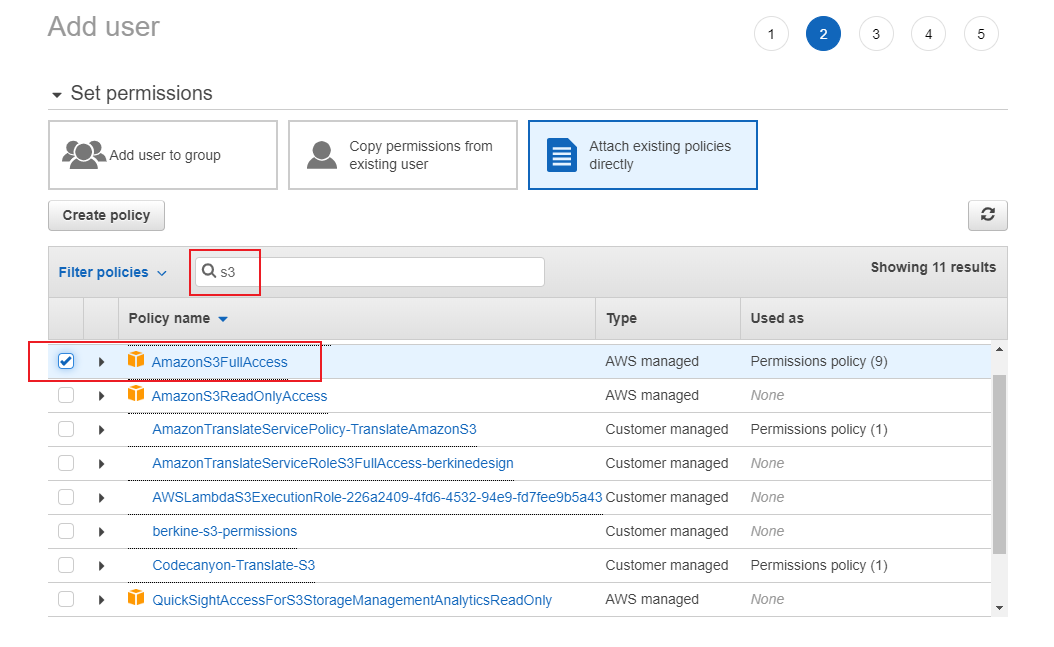
Search for S3 and choose S3 Full Access permissions(if you are good with policies, you can create your own custom S3 Access Policies)
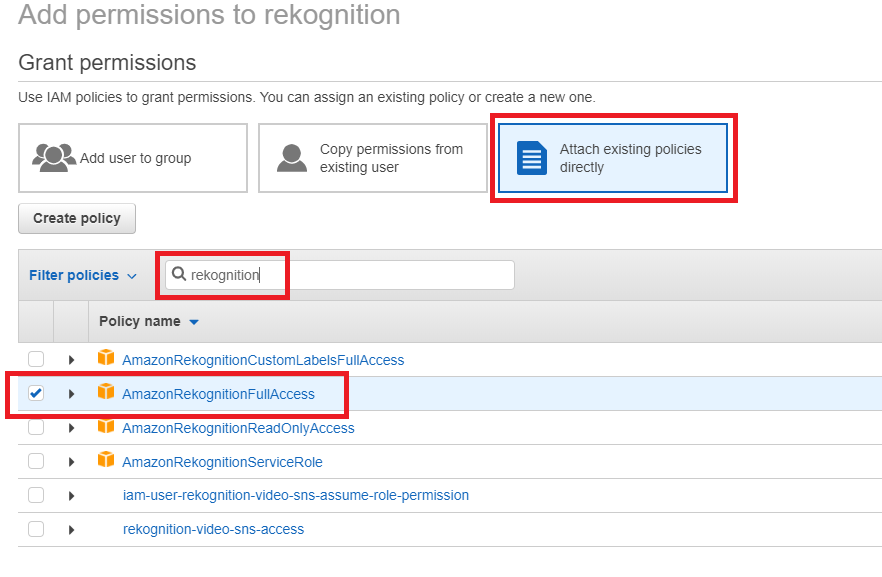
Search for Rekognition and choose Rekognition Full Access permissions
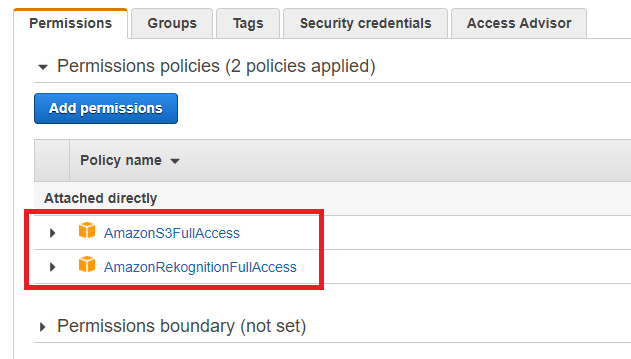
Continue until they are added, on your last step you shoul see both of the policies about to be added to the user
Step 3
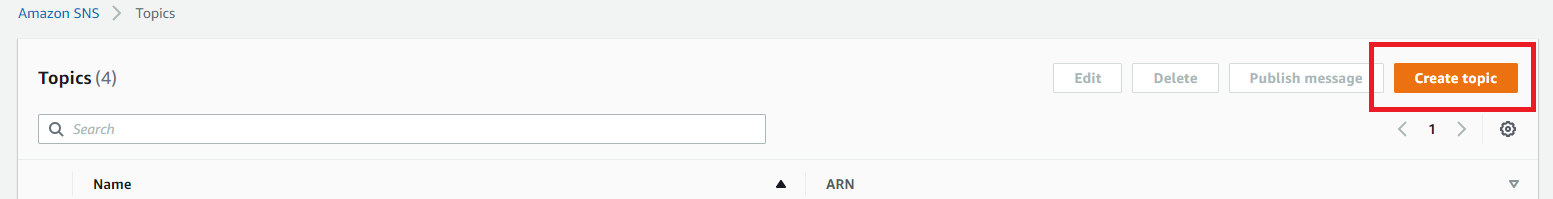
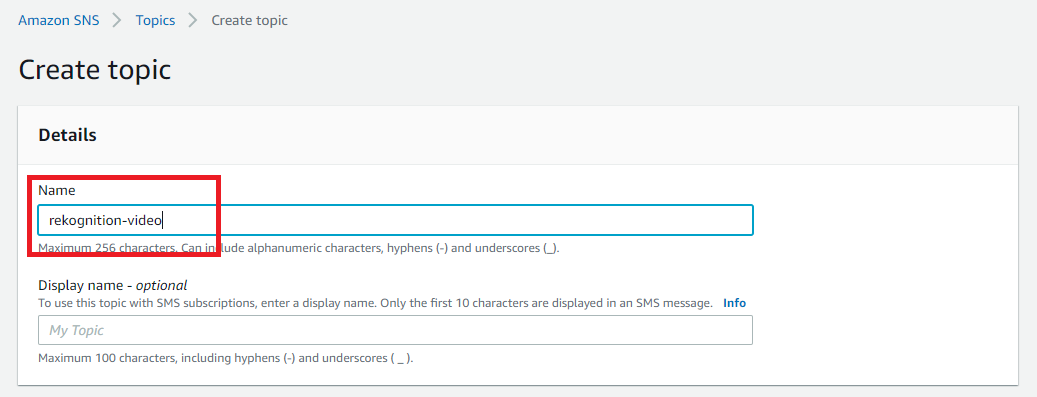
Create SNS Topic, Rekognition will post Job Statuses to this Topic
Go to SNS Service and select Create Topic
Provide a name to your SNS Topic and click Create
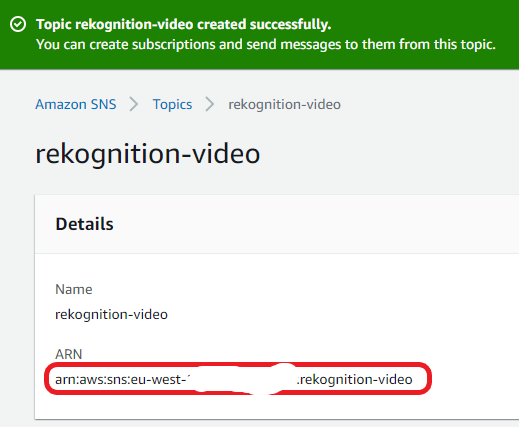
On the summary page, copy SNS Topic ARN, you will need it in Step 4 when we will be create policy
Step 4
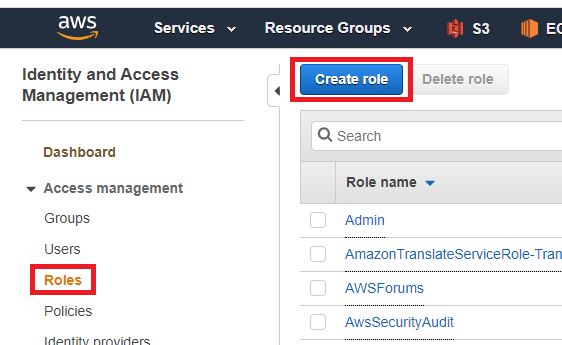
Now we need to create a Role for for the app that can call Rekognition
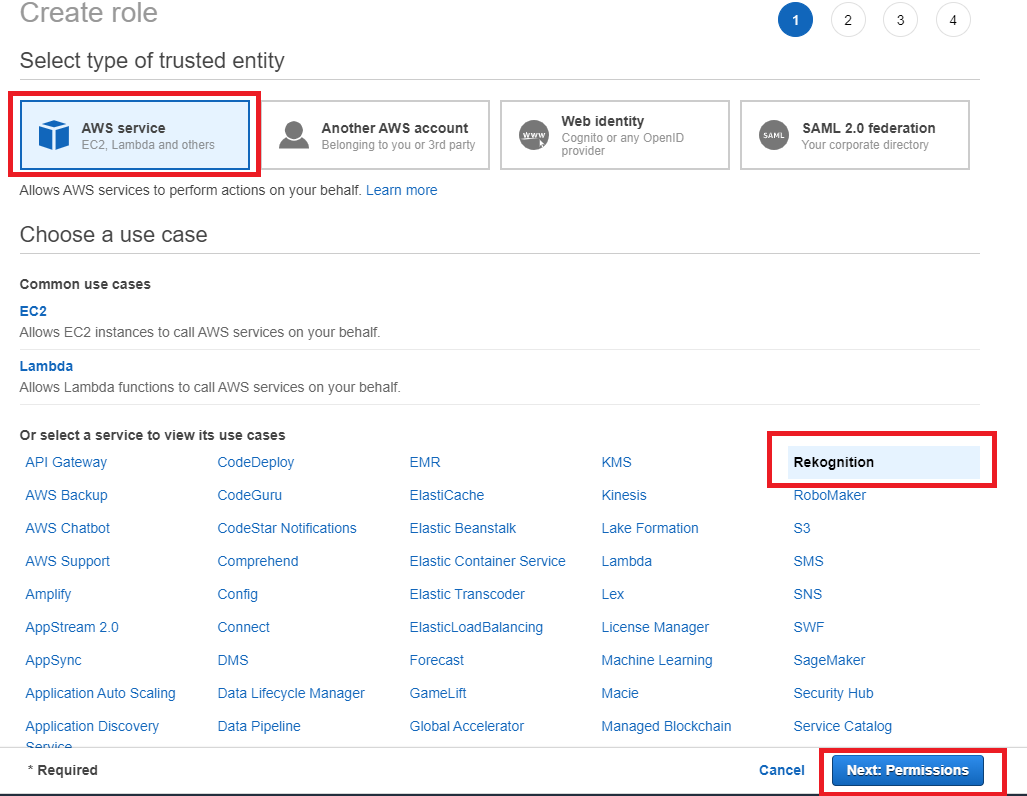
Go to IAM Services and select Role, select Role - Create Role
Select Rekognitin, click Next:Permissions
Provide a Role name so that you can find it afterwards, click Create Role
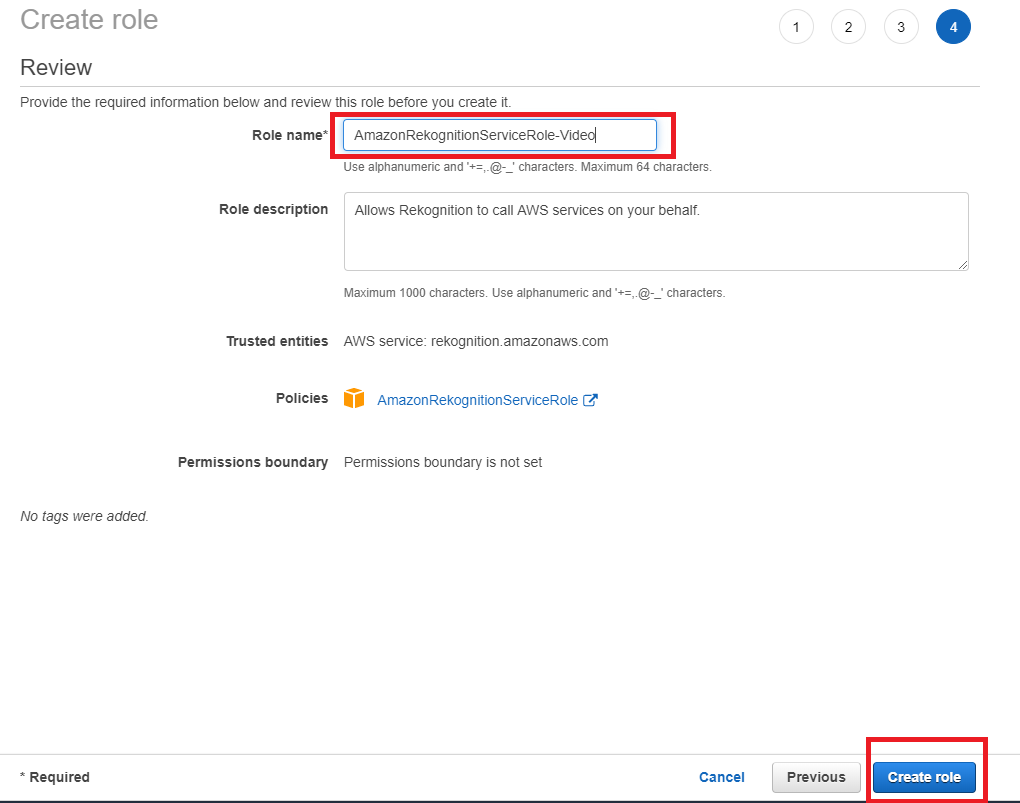
Search for newly created Role - you can search by role name that you set, select the role.
Copy Role ARN
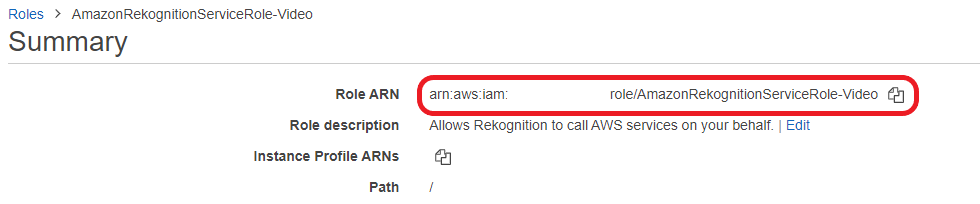
You will need copied Role ARN in Step 5.
Now we need to create policy that we will add to this Role, this policy will let Rekognition interact with the SNS topic we created in Step 3.
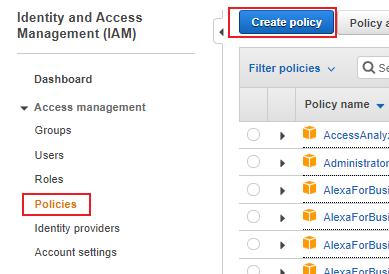
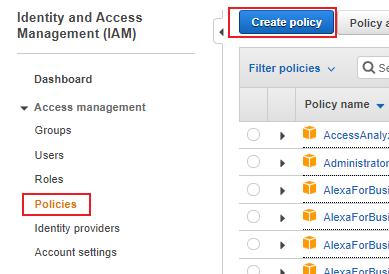
Select Policy - Create Policy
Select JSON tab and copy paste code below, instead of XXXXXXXXXX copy and paste the SNS Topic ARN that you create in Step3
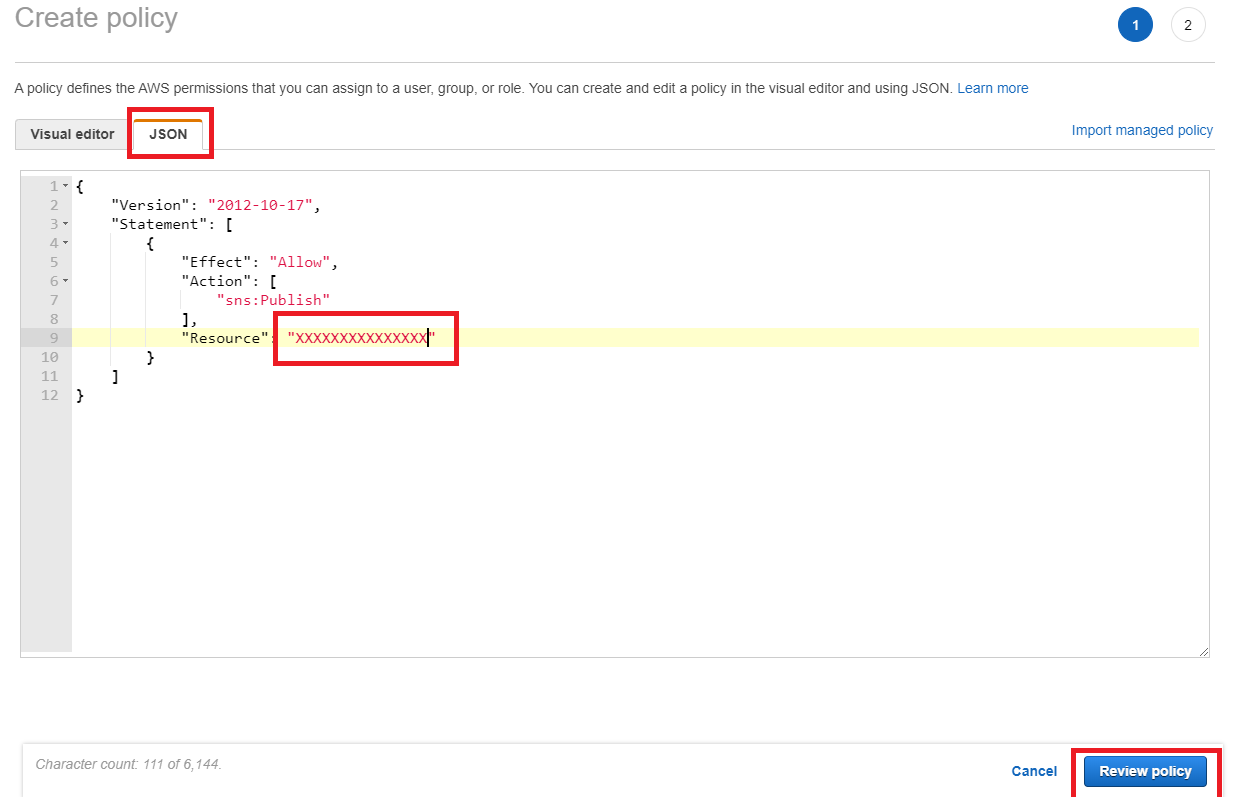
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Action": [ "sns:Publish" ], "Resource": "XXXXXXXXXXXXXXX" } ] }Provide a name to you policy and click Create Policy
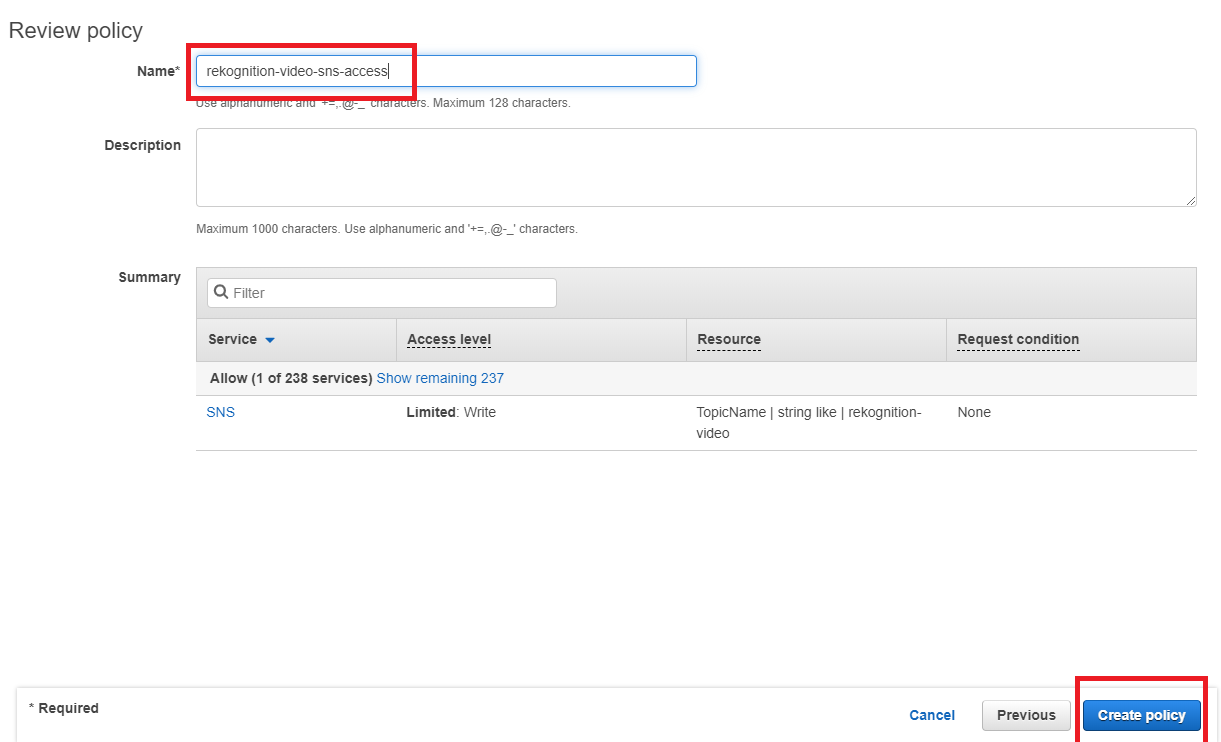
Attach this policy to the role that you created earlier, so that it looks like this in the end
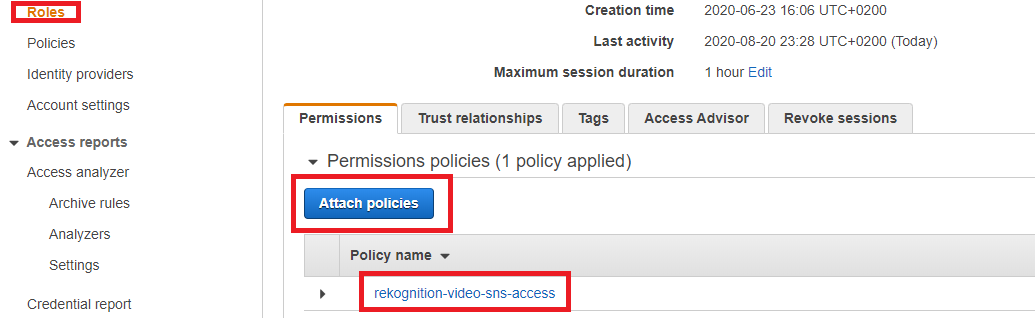
Step 5
By itself your Rekognitin Video code cannot call assigned Role from Step 4, that is why we need assume the role permission. It will be last step of IAM user configuration
Select Policy - Create Policy
Select JSON tab and copy paste code below, instead of XXXXXXXXXX copy and paste the Role ARN that you create in Step 4
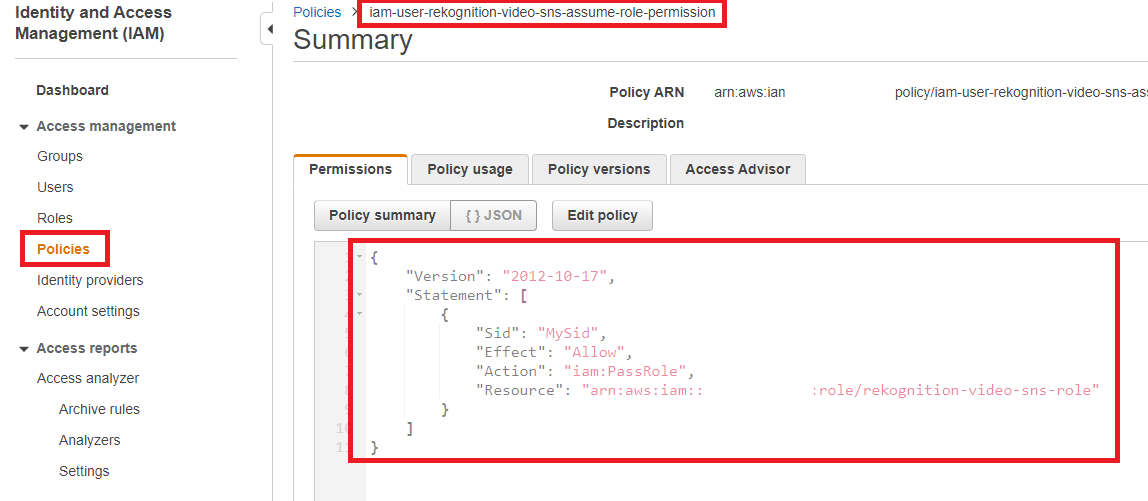
{ "Version": "2012-10-17", "Statement": [ { "Sid": "MySid", "Effect": "Allow", "Action": "iam:PassRole", "Resource": "XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX" } ] }Assing this policy to the IAM user that you created in Step 2, you should have all 3 policies attached that are listed below
Step 6
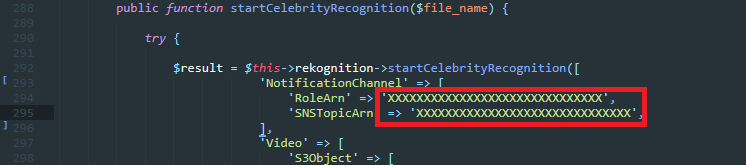
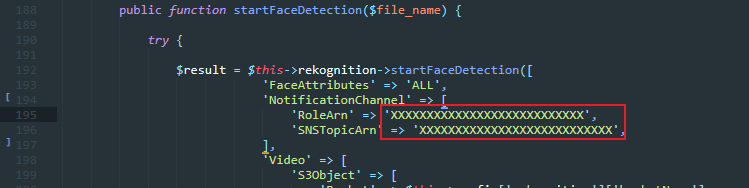
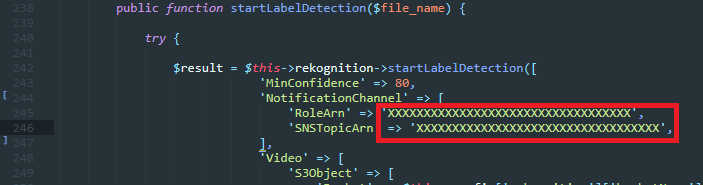
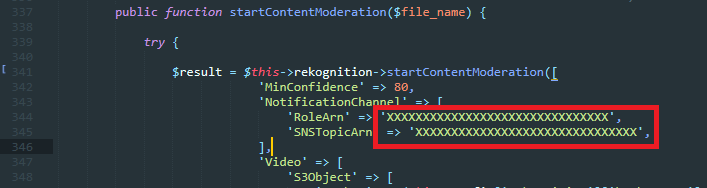
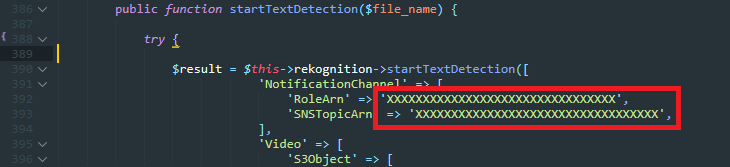
For the Rekognition.php you will need to include Role ARN that you created in Step 4 and also SNS Topic ARN that you created in Step 3
Include Role ARN and Topic ARN to all 5 Rekognition Video Functions.
Step 7
To use Webcam for Facial Image Analysis, you will need to have SSL CA certification enabled at your server, otherwise browsers these days will not allow you to use client webcam connections if you are not using https connection.
If you need help with setting up a free SSL CA certificate, please refer to this how to tutorial at youtube by Atiqur Rahman - Link
How to Create S3 Bucket
Before you can upload data to Amazon S3, you must create a bucket in one of the AWS Regions to store your data in. After you create a bucket, you can upload an unlimited number of data objects to the bucket.
A bucket is owned by the AWS account that created it. By default, you can create up to 100 buckets in each of your AWS accounts. If you need additional buckets, you can increase your account bucket limit to a maximum of 1,000 buckets by submitting a service limit increase. For information about how to increase your bucket limit, see AWS Service Limits in the AWS General Reference.
Buckets have configuration properties, including their geographical region, who has access to the objects in the bucket, and other metadata.
To create an S3 bucket
-
Sign in to the AWS Management Console and open the Amazon S3 console at https://console.aws.amazon.com/s3/.
-
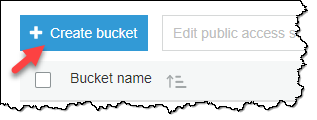
Choose Create bucket.
-
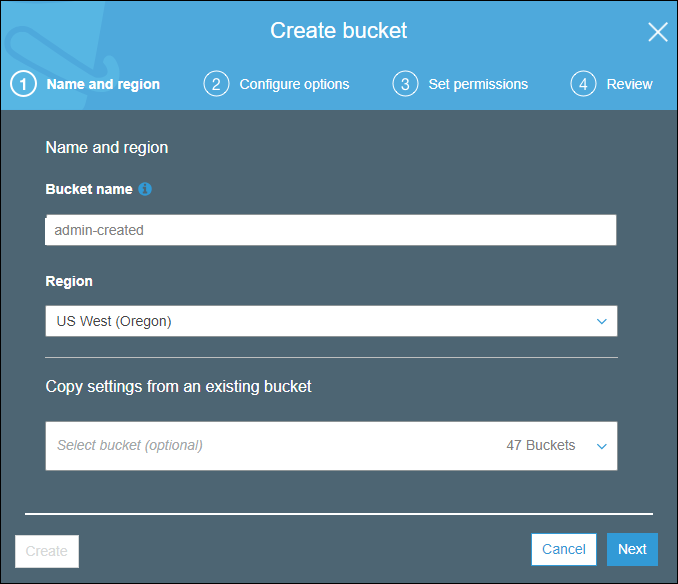
On the Name and region page, type a name for your bucket and choose the AWS Region where you want the bucket to reside. Complete the fields on this page as follows:
-
For Bucket name, type a unique DNS-compliant name for your new bucket. Follow these naming guidelines:
-
The name must be unique across all existing bucket names in Amazon S3.
-
The name must not contain uppercase characters.
-
The name must start with a lowercase letter or number.
-
The name must be between 3 and 63 characters long.
-
After you create the bucket you cannot change the name, so choose wisely.
-
Choose a bucket name that reflects the objects in the bucket because the bucket name is visible in the URL that points to the objects that you're going to put in your bucket.
-
-
For Region, choose the AWS Region where you want the bucket to reside. Choose a Region close to you to minimize latency and costs, or to address regulatory requirements. Objects stored in a Region never leave that Region unless you explicitly transfer them to another Region. For a list of Amazon S3 AWS Regions, see Regions and Endpoints in the Amazon Web Services General Reference.
-
(Optional) If you have already set up a bucket that has the same settings that you want to use for the new bucket that you want to create, you can set it up quickly by choosing Copy settings from an existing bucket, and then choosing the bucket whose settings you want to copy.
The settings for the following bucket properties are copied: versioning, tags, and logging.
-
Do one of the following:
-
If you copied settings from another bucket, choose Create. You're done, so skip the following steps.
-
If not, choose Next.
-
-
-
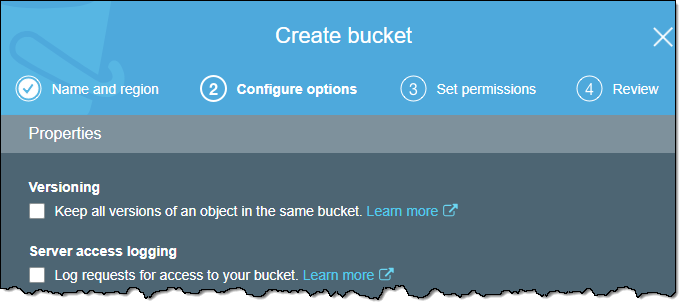
On the Configure options page, you can configure the following properties and Amazon CloudWatch metrics for the bucket. Or, you can configure these properties and CloudWatch metrics later, after you create the bucket.
-
Versioning
Select Keep all versions of an object in the same bucket. to enable object versioning for the bucket.
-
Server access logging
Select Log requests for access to your bucket. to enable server access logging on the bucket. Server access logging provides detailed records for the requests that are made to your bucket.
-
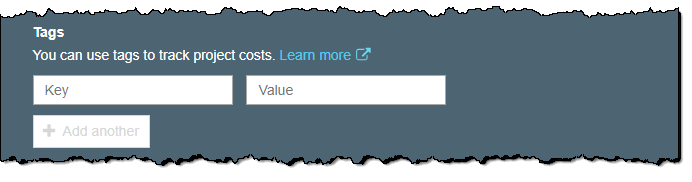
Tags
You can use cost allocation bucket tags to annotate billing for your use of a bucket. Each tag is a key-value pair that represents a label that you assign to a bucket.
To add a tag, enter a Key and a Value. Choose Add another to add another tag.
-
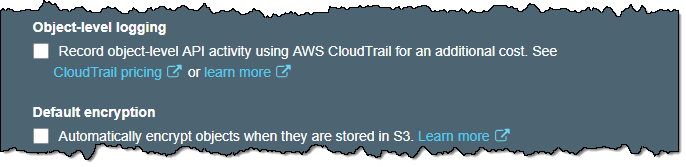
Object-level logging
Select Record object-level API activity by using CloudTrail for an additional cost to enable object-level logging with CloudTrail.
-
Default encryption
Select Automatically encrypt objects when they are stored in S3 to enable default encryption for the bucket. You can enable default encryption for a bucket so that all objects are encrypted when they are stored in the bucket.
-
Object lock
Select Permanently allow objects in this bucket to be locked if you want to be able to lock objects in the bucket. Object lock requires that you enable versioning on the bucket.
-
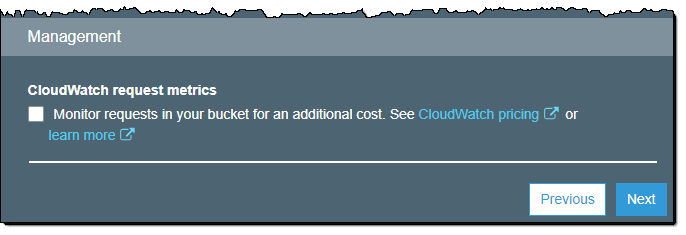
CloudWatch request metrics
Select Monitor requests in your bucket for an additional cost. to configure CloudWatch request metrics for the bucket.
-
-
Choose Next.
-
On the Set permissions page, you manage the permissions that are set on the bucket that you are creating.
Under Block public access (bucket settings), we recommend that you do not change the default settings that are listed under Block all public access. You can change the permissions after you create the bucket.
Warning
We highly recommend that you keep the default access settings for blocking public access to the bucket that you are creating. Public access means that anyone in the world can access the objects in the bucket.
If you intend to use the bucket to store Amazon S3 server access logs, in the Manage system permissions list, choose Grant Amazon S3 Log Delivery group write access to this bucket.
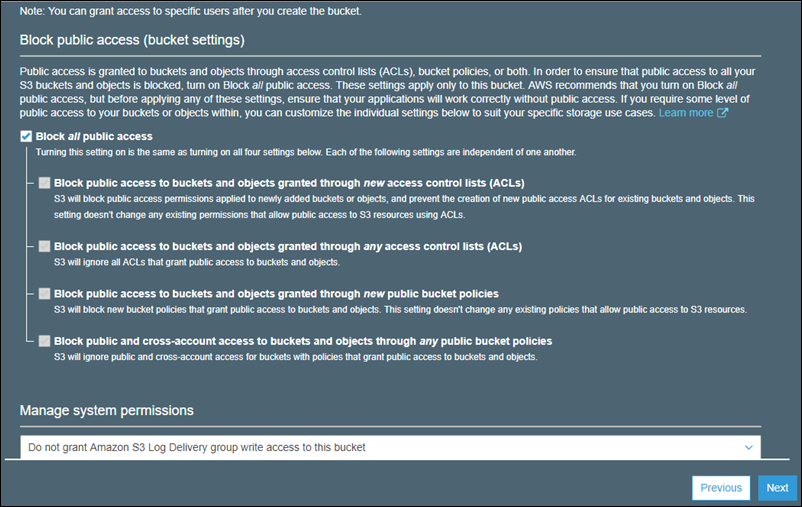
When you're done configuring permissions on the bucket, choose Next.
-
On the Review page, verify the settings. If you want to change something, choose Edit. If your current settings are correct, choose Create bucket.
Creating AWS IAM Users (via AWS Console)
You can use the AWS Management Console to create IAM users.
To create one or more IAM users (console)
-
Sign in to the AWS Management Console and open the IAM console at https://console.aws.amazon.com/iam/.
-
In the navigation pane, choose Users and then choose Add user.
-
Type the user name for the new user. This is the sign-in name for AWS. If you want to add more than one user at the same time, choose Add another user for each additional user and type their user names. You can add up to 10 users at one time.
Note
User names can be a combination of up to 64 letters, digits, and these characters: plus (+), equal (=), comma (,), period (.), at sign (@), and hyphen (-). Names must be unique within an account. They are not distinguished by case. For example, you cannot create two users named TESTUSER and testuser.
-
Select the type of access this set of users will have. You can select programmatic access, access to the AWS Management Console, or both.
-
Select Programmatic access if the users require access to the API, AWS CLI, or Tools for Windows PowerShell. This creates an access key for each new user. You can view or download the access keys when you get to the Final page.
-
Select AWS Management Console access if the users require access to the AWS Management Console. This creates a password for each new user.
-
For Console password, choose one of the following:
-
Autogenerated password. Each user gets a randomly generated password that meets the account password policy in effect (if any). You can view or download the passwords when you get to the Final page.
-
Custom password. Each user is assigned the password that you type in the box.
-
-
-
Choose Next: Permissions.
-
On the Set permissions page, specify how you want to assign permissions to this set of new users. Choose one of the following three options:
-
Add user to group. Choose this option if you want to assign the users to one or more groups that already have permissions policies. IAM displays a list of the groups in your account, along with their attached policies. You can select one or more existing groups, or choose Create group to create a new group.
-
Copy permissions from existing user. Choose this option to copy all of the group memberships, attached managed policies, embedded inline policies, and any existing permissions boundaries from an existing user to the new users. IAM displays a list of the users in your account. Select the one whose permissions most closely match the needs of your new users.
-
Attach existing policies to user directly. Choose this option to see a list of the AWS managed and customer managed policies in your account. Select the policies that you want to attach to the new users or choose Create policy to open a new browser tab and create a new policy from scratch. After you create the policy, close that tab and return to your original tab to add the policy to the new user. As a best practice, we recommend that you instead attach your policies to a group and then make users members of the appropriate groups.
-
-
(Optional) Set a permissions boundary. This is an advanced feature.
Open the Set permissions boundary section and choose Use a permissions boundary to control the maximum user permissions. IAM displays a list of the AWS managed and customer managed policies in your account. Select the policy to use for the permissions boundary or choose Create policy to open a new browser tab and create a new policy from scratch.
-
Choose Next: Tags.
-
(Optional) Add metadata to the user by attaching tags as key-value pairs.
-
Choose Next: Review to see all of the choices you made up to this point. When you are ready to proceed, choose Create user.
-
To view the users' access keys (access key IDs and secret access keys), choose Show next to each password and access key that you want to see. To save the access keys, choose Download .csv and then save the file to a safe location.
Important
This is your only opportunity to view or download the secret access keys, and you must provide this information to your users before they can use the AWS API. Save the user's new access key ID and secret access key in a safe and secure place. You will not have access to the secret keys again after this step.
-
Provide each user with his or her credentials. On the final page you can choose Send email next to each user. Your local mail client opens with a draft that you can customize and send. The email template includes the following details to each user:
Support
Support includes bugs fixing, and general problem solving with features explained on the template’s official sales page.
Support does not include:
- solving problems for plugins not packaged with our framework and templates;
- plugins integration;
- adding new features or extending the features currently available;
- any type of modification or customization.

Once again, thank you so much for purchasing this Amazon Rekognition Video Application. As I said at the beginning, I'd be glad to help you if you have any questions relating to this template. No guarantees, but I'll do my best to assist. If you have a more general question relating to the templates on CodeCanyon, you might consider visiting the forums and asking your question in the "Item Discussion" section.
Regards,
Berkine